Identity Platform (IP) – software for building a single authentication center for internal and external users, devices and services. Identity Platform delivers the functions for centralized management of accounts and provides Single Sign-On (SSO) technology.
Which companies is this solution for?
- Large companies regardless of their activity type, which have a lot of different software in the internal IT-infrastructure, and which have a need to maintain a number of users accounts with passwords: In this case Identity Platform acts as a single user account center. All programs are configured for Identity Platform authentication.
- Banks that want to join the open banking interface environment: Identity Platform that supports the security profiles in compliance with Bank of Russia standards is used in banks as an authorization server.
- Companies, which use OAuth 2.0 or OpenID Connect software and want to add business logic to the registration/authentication of users, devices, or services: for example, any mobile applications or ATMs.
- Site owners who wish to authenticate their clients through external providers, for example, Unified Identification and Authentication System in Russia.
The license price and free version of the software are available upon request. Please fill in the feedback form at the bottom of the page or email us at sales@ekassir.com.
Implementation results
-
Centralized system
of employees and clients
authentication -
Services protection via the
combination Identity Gateway +
Access Manager -
Authentication plugins
-
Providing controlled access to the company API
Creating a single-point, centralized user accounts storage.
- Administrator update Identity Platform settings, so the user can start using their company’s apps in according to specified rights, roles and groups.
- Managing password policies, specifying a password complexity, password expiration time. No apps where one can log in with a weak password (e.g, 123456).
- User has no need to memorize credentials for each app. With Single Sign-On technology a user can enter their login and password only once and start working will all apps.
As a result:
- Efficiency of the information security officer work starts increasing
- Number of calls and messages to support service gets reduced
- Ensures less risk of the information security, as the apps no longer store the records of fired employees, which accidentally were not blocked
- All information about user actions is collected in a single place due to the centralized audit
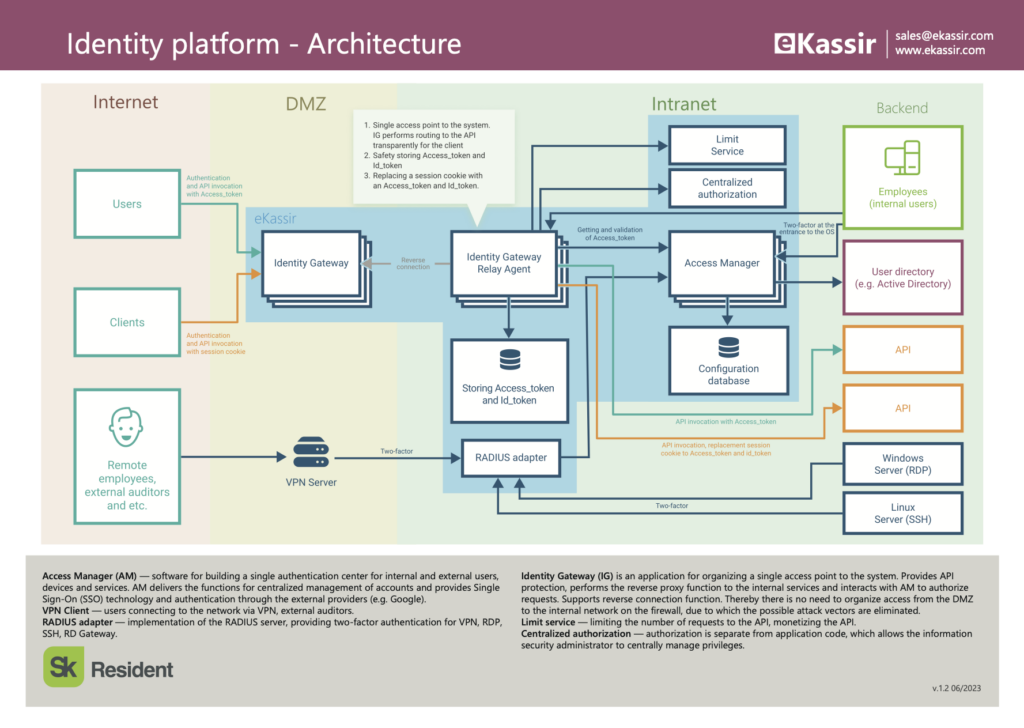
By protecting the services with the combination of Access Manager and Identity Gateway you get the reliable infrastructure safety. Protected services require presence of an access token in user request, so token safety needs special attention. Identity Gateway provides access tokens storage, so that the tokens do not get out of the IT-infrastructure of your company.
As a result:
- Compromise risks for access tokens gets decreased, as the tokens are not transferred to services users
- Your services are protected with access tokens
- Differentiation of the access level depending on the content of access_token.
In case when your app needs special logic for registration or authentication, any scenario can be implemented with authentication plugins. It is possible to apply authentication for users and clients, mobile devices and ATMs.
As a result:
- Authentication plugins provide your business requirements for any type of authentication
Access Manager allows you to control access to the company's internal APIs by external partners:
- you can quickly connect the new users or block existing ones;
- you can set an access level for each partners in particular; for example, a privileged client could obtain the read and customize permission but other clients could only use reading rights.
Features
Cutting-edge technologies stack
System core is created with.NET Core; administrator’s UI and personal area is written with ReactJS
Cross-platform solutions
Identity Platform is written with .NET Core, so it works both in Windows and Linux
Scalability
Identity Platform supports horizontal scaling (servers cluster can be configured)
Virtualization and Docker support
Identity Platform works on physical and virtual as well as in Docker container
Extensibility
Identity Platform is implemented with module approach; API for designing extension modules is also provided
Standards support
IP supports industry security standards:
- OAuth 2.0
- Open ID Connect
No UI mode
IP can work when administrator’s UI is turned off; in this situation configuring is performed via static files and administrative operations – via admin API
Security
Support connections only by secure HTTPS protocol. Trusted X.509 certificate should be installed for IP server authentication
UI customization
Identity Platform components can be make in one visual design.
- Entrance page
- Self-service area
- Administrative interface
- Consent/Error/Exit pages
Success stories
Additional materials
Questions
Request a call
Leave your contact details to get more information about eKassir solutions, implementation, or anything else from our team